4530
4530
PART 1: Enable the “Windows Remote Management” (WinRM) Service on the Endpoints.
Note: Since we need this service running on all the endpoints that we plan to have forward events it is recommended to use Group Policy to enable this setting.
- To enable this service using Group Policy first create and link a GPO to the domain or OU where the computers (endpoints) live, give this a GPO a descriptive name, (i.e. “Event Log Forwarding Setup”).
- Next edit the GPO, expand Computer Configuration > Preferences > Control Panel Settings > Services, then right click “Services” and choose “New > Service”
- Under the “New Service Properties” > “General” tab > “Service name:” click the ellipses (…) and browse for the WinRM service, then with the WinRM service highlighted, click “Select”.
- Set the “Service action:” to “Start service” then click “Ok”.
PART 2: Allow the “Local Network Service” to access the event logs.
- In the same GPO as above, expand Computer Configuration > Policies > Windows Settings > Security Settings > Restricted Groups, then right-click “Restricted Groups” and select “Add Group”, then type in “Event Log Readers” and click “Ok”.
- Next right-click on the “Event Log Readers” group and select “Properties”, then add “NETWORK SERVICE” under “Members of this group:”, and click “Ok”.
PART 3: Setting up the Event Forwarding Subscription
- In the same GPO as above, expand Computer Configuration > Policies > Administrative Templates > Windows Components > Event Forwarding, then double-click “Configure target Subscription Manager”, select the radio button for "Enabled" then click “Show...”
- Under “Show Contents” configure the following:
Note:
- Replace “YourServerFQDN” with the Fully Qualified Domain Name (FQDN) of your central collection machine (the one you want to forward events to). For example, if your server name was dc2016.fabrikam.com you would use:
SERVER=http://DC2016.FABRIKAM.COM:5985/wsman/SubscriptionManager/WEC
- For HTTPS protocol use:
SERVER=https://<FQDN of the collector>:5986/wsman/SubscriptionManager/WEC,Refresh=<Refresh interval in seconds>,IssuerCA=<Thumb print of the client authentication certificate>.
- “Refresh=60” is optional and equals 60 seconds, this value should only be used for testing. Once everything is working remove the “,Refresh=60” or don’t use it to begin with and instead wait for events to be forwarded (I believe the default interval is 15 minutes). Best Practices info from Microsoft: https://support.microsoft.com/en-us/help/4494356/best-practice-eventlog-forwarding-performance
- Replace “YourServerFQDN” with the Fully Qualified Domain Name (FQDN) of your central collection machine (the one you want to forward events to). For example, if your server name was dc2016.fabrikam.com you would use:
- On the central collection machine or server (the one you want to forward events to) open Event Viewer then click on Subscriptions. If shown the message below, click “Yes”.
- Now right click “Subscriptions” and choose “Create Subscription…”.
- Give the Subscription a name (i.e. PolicyPak Interesting Events), then select the “Source computer initiated” radio button, and click the “Select Computer Groups” button.
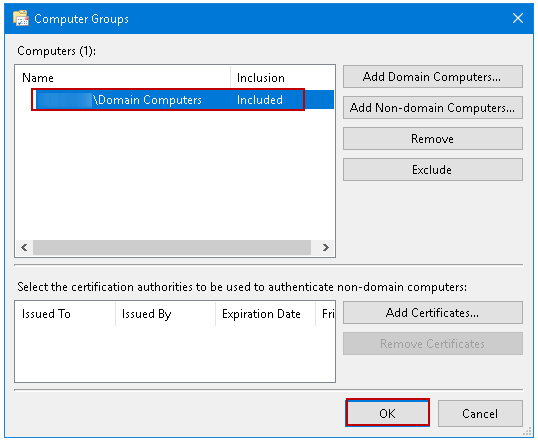
- Under “Select Computer Groups” click “Add Domain Computers…” then add the “Domain Computers” group, and click “Ok”.
- Next click “Select Events…”
- Under the “Select Events” if you happen to have the PolicyPak Client Side Extensions (CSE) installed you can select the “By Log” radio button then use the drop down under “Event Sources:” to find “PolicyPak Least Privilege Manager Client – Operational” and place a check box next to it, then click “Ok”.
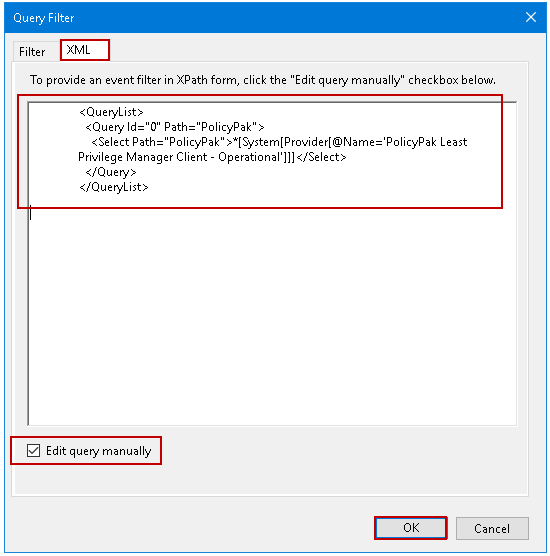
If done correctly you should now see a screen similar to below:Note: If you don’t have the CSE installed, select the “XML” tab, then check the “Edit query manually” check box at the bottom before pasting in the query below and clicking “Ok”. You will not be able to use the Filter tab after editing the XML query manually.
<QueryList>
<Query Id="0" Path="PolicyPak">
<Select Path="PolicyPak">*[System[Provider[@Name='PolicyPak Least Privilege Manager Client - Operational']]]</Select>
</Query>
</QueryList>Note: Once you click “Ok” the text will be formatted correctly and aligned on the left.
- Lastly, run “gpupdate /force” on a test computer and then wait until the 60 seconds or 15-minute interval has passed before clicking refresh in the Subscriptions Window or “Forwarded Events” log. If any PolicyPak Least Privilege Operational events have occurred within that interval and everything else is working you should start to see computers showing up under the “Source Computers” column in the subscription, and start to see events from the source computers showing up under the “Forwarded Events” log.