4138
4138
Method 1 (Recommended): Elevating the underlying .EXE
-
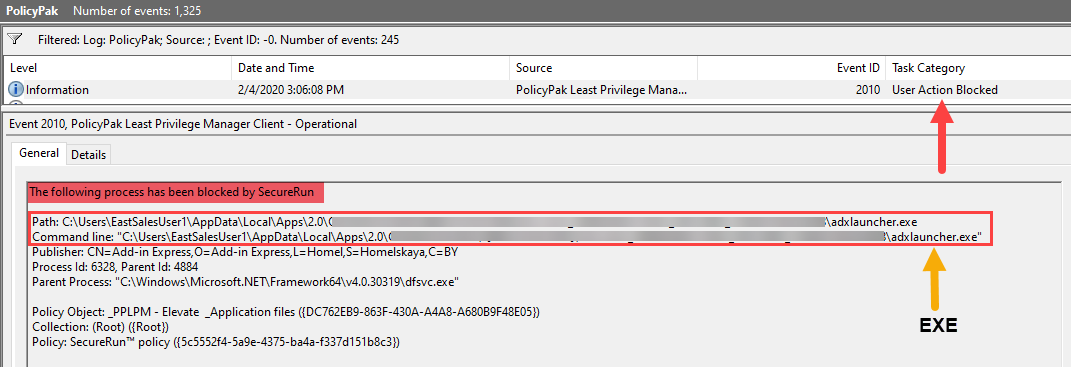
Look in the PolicyPak Event log for the blocked event to discover the name of the EXE being blocked:
-
Create an EXE elevation combo rule in Least Privilege Manage for the EXE being blocked.
TIP: The more conditions evaluated the more secure the rule will be. See this video for more details: https://kb.policypak.com/kb/article/626
-
Apply the policy and then verify using the PolicyPak event log that the application is being Elevated.
Method 2: Elevating RUNDLL32.exe and the .APPLICATION exactly
-
Immediately after receiving the BLOCKED message (launch the application again if needed) look in the Least Privilege Manager Log
PPService.logwhich can be found here by default:%programdata%\PolicyPak\PolicyPak Least Privilege Manager\ppService.log(i.e.C:\ProgramData\PolicyPak\PolicyPak Least Privilege Manager\ppService.log)Note: Reason we look immediately in the log is so that we know which ppservice().log file to look in, ppservice.log is the latest log, and ppservice(n).log files are the rolled over logs.
-
Open the ppservice.log in notepad (or any text editor) then scroll all the way to the bottom, then start searching from the bottom upwards for the text “.application”.
-
What we are looking for is the entire command-line used to launch the .application. See below for example:
Using the example above our entire command-line would be:
"C:\Windows\System32\rundll32.exe" "C:\Windows\System32\dfshim.dll",ShOpenVerbApplication C:\Users\EastSalesUser1\Desktop\test.application -
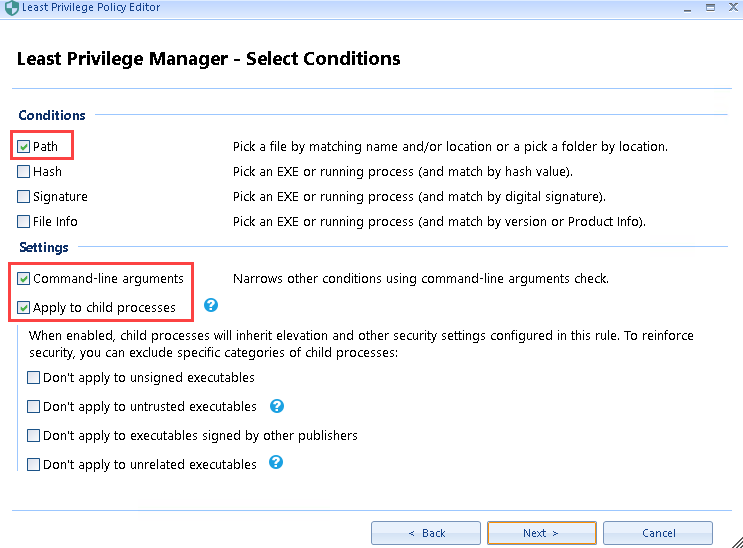
Now we are going to create an EXE combo elevation rule using PATH, and also check the two settings for “Command-line arguments” and “Apply to child processes” before clicking “Next”.
-
Enter “*\EXE” for the PATH, replace EXE with the name of the executable mentioned in the command-line from the ppservice.log relevant to your environment, then click “Next”.
In my example, the EXE name is “Rundll32.exe”. -
At the next screen (click ok on the command-line arguments cannot be empty warning if necessary) then copy and paste the entire command-line from the ppservice.log file into the “Arguments” section, and ensure that “Strict equality” and “Ignore arguments case” are both checked. Then click “Next” then “Finish” to save the rule.
-
Lastly, apply the policy then verify using the PolicyPak event log that the application is being Elevated.